LoJacking
Some crackers hijack devices - like hijacking a car. The device gets somewhat unusable or uses all its battery and CPU/NET power to perform zombie commands for the attacker.
I don’t hijack devices, but I lo-jack mine. Lo-jacking is a neologism invented by the netsec community AFAIK. My devices regularly phone home to signal their location. They don’t activate the GPS so that the burglar does not get alerted. They don’t open a browser or a url so even the tech-savvy guy does not get alerted. Using a proxy or a VPN won’t help either.
- I have a custom bootloader to check the application presence
- The auto-activated application starts an android service
- The service monitors passive location updates and exfiltrates them through DNS lookups
- Killing the application won’t help - auto-restart
Typical data phoned home. The DNS subpart is modified to prevent the floating point dot notation to interfere.

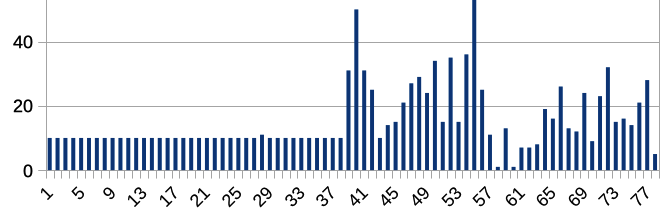
Typical “phone home” rate. Android respects the requested timer period “every 10 minutes” .. except when it decides to stop/tamper with/delay/doze or whatever. Heavy load on the device will also trigger this behaviour. The rate is fair enough and ensures I know on a regular basis where the device is (as soon as it is up).